Unseen Web3 Hackers Exploit Phishing to Steal $464M in Q1—Is Your Crypto Safe?
Ever wonder if the revolution in Web3 just handed hackers the keys to the kingdom? Turns out, the first quarter of 2026 wasn’t exactly a win for decentralization security, with Web3 projects bleeding a staggering $464.5 million to hacks and scams. What’s wild is the shift from headline-grabbing mega hacks to a scatter of mid-sized, sneaky breaches—like that jaw-dropping $282 million hardware wallet scam in January swallowing a huge chunk of the damage. These losses, while painful, mark the second-lowest quarterly hit since 2023, but they unveil a sneaky trend: the biggest vulnerabilities aren’t crawling out of the blockchain code itself, but lurking in the shadowy operational shadows that audits just don’t spotlight. Plus, as regulators from the EU to Dubai get serious about continuous security and enforce rapid incident responses, it’s clear the game’s evolving—fast. Curious how phishing, fake VC calls, and even legacy code bugs continue to trip up projects despite heavy audits? And what about the human element—because, let’s face it, the best firewalls won’t save you from well-crafted social engineering attacks. Strap in, because the landscape of crypto security just got a whole lot messier. LEARN MORE.
Web3 projects lost $464.5 million to hacks and scams in the first quarter of 2026, while multi-billion-dollar “mega hacks” gave way to a larger number of mid-sized incidents, according to blockchain security company Hacken.
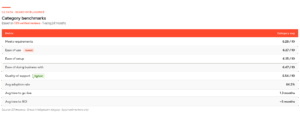
According to Hacken’s Q1 2026 report, phishing and social engineering attacks dominated the period, accounting for $306 million in losses in a quarter that saw 43 incidents overall. A single $282 million hardware wallet scam in January was responsible for 81% of the quarter’s damage.
Smart contract exploits totaled $86.2 million, with access control failures, including compromised keys and cloud services, driving an additional $71.9 million in losses.
The losses place this quarter as the second-lowest first quarter since 2023, with the absence of a single mega hack on the scale of Bybit, which lost $1.46 billion in Q1 2025, the primary driver of the year-over-year decline.
Hacken’s incident mapping shows the largest failures increasingly occurring outside onchain code, in operational and infrastructure layers that traditional audits rarely touch. Yev Broshevan, chief executive and co-founder at Hacken, told Cointelegraph the most expensive failures “happen outside the code layer entirely.”
Related: Aethir halts bridge exploit, promises compensation after $90K loss
According to Hacken, that shift is drawing greater scrutiny from regulators and institutional counterparties, with frameworks such as the Markets in Crypto-Assets Regulation (MiCA) and Digital Operational Resilience Act (DORA) in the European Union moving further into enforcement and raising expectations around continuous security monitoring and incident response.
Legacy code, fake VC calls and key compromises
Broshevan pointed to $306 million in phishing, a $40 million North Korea-linked fake venture capitalist (VC) call against Step Finance, and a $25 million AWS key management service compromise at Resolv Labs. Even where smart contracts were at fault, the costliest bugs often sat in legacy deployments and known vulnerability classes. Truebit lost $26.4 million to a bug in a Solidity contract deployed around five years ago, while Venus Protocol was hit by a donation attack pattern documented since 2022.

Six audited projects, including Resolv with 18 audits and Venus with five separate firms, still accounted for $37.7 million in losses. On average, that was more than their unaudited peers because higher total value locked (TVL) protocols attract more sophisticated attackers and exploits.
Global watchdogs harden incident response expectations
In Q1, MiCA and DORA in the EU shifted further into active enforcement, Dubai’s regulator, the Virtual Assets Regulatory Authority, tightened expectations around its Technology and Information Rulebook, Singapore enforced Basel-aligned capital and one-hour incident notification rules, and the United Arab Emirates’ new Capital Market Authority took over federal digital asset oversight with broader powers and higher penalties.

Related: Crypto hackers steal $169M from 34 DeFi protocols in Q1: DefiLlama
Hacken ties those regimes to a new benchmark for “regulator-ready” stacks that includes proof-of-reserves attestations backed by daily internal reconciliation, 24/7 onchain monitoring across treasury wallets and privileged roles, automated circuit-breakers on minting and governance functions and incident notification clocks calibrated to the strictest applicable standard.
The report highlights “realistic” targets of awareness within 24 hours, labeling within four hours, and blocking in 30 seconds, with “aspirational” goals as low as 10 minutes for detection and 1 second to block, based on guidance from Global Ledger’s 2025 Laundering Race data.
At the human layer, Hacken flags North Korean clusters as the most consistent operational threat, with Step Finance’s $40 million loss and Bitrefill’s infrastructure breach extending a playbook of fake VC outreach, malicious video call tooling and compromised employee endpoints that extracted roughly $2.04 billion from the sector in 2025.
Magazine: XRP yet to ‘price in’ 3 bullish catalysts, Bitcoin to $80K? Trade Secrets